SKY PULSE NEWS
LOCATION: MILWAUKEE HUB | TUNNEL: TOKYO RELAY | TARGET: KOLKATA CLUSTER
URGENT: INFRASTRUCTURE UNMASKING IN PROGRESS
INVESTIGATION: The Kolkata "Ghost" Host
On April 26, 2026, Sky Pulse News identified a high-density scam operation leveraging Google Cloud infrastructure. While appearing as standard mail servers, deep-packet inspection revealed a hidden Command & Control (C2) node.
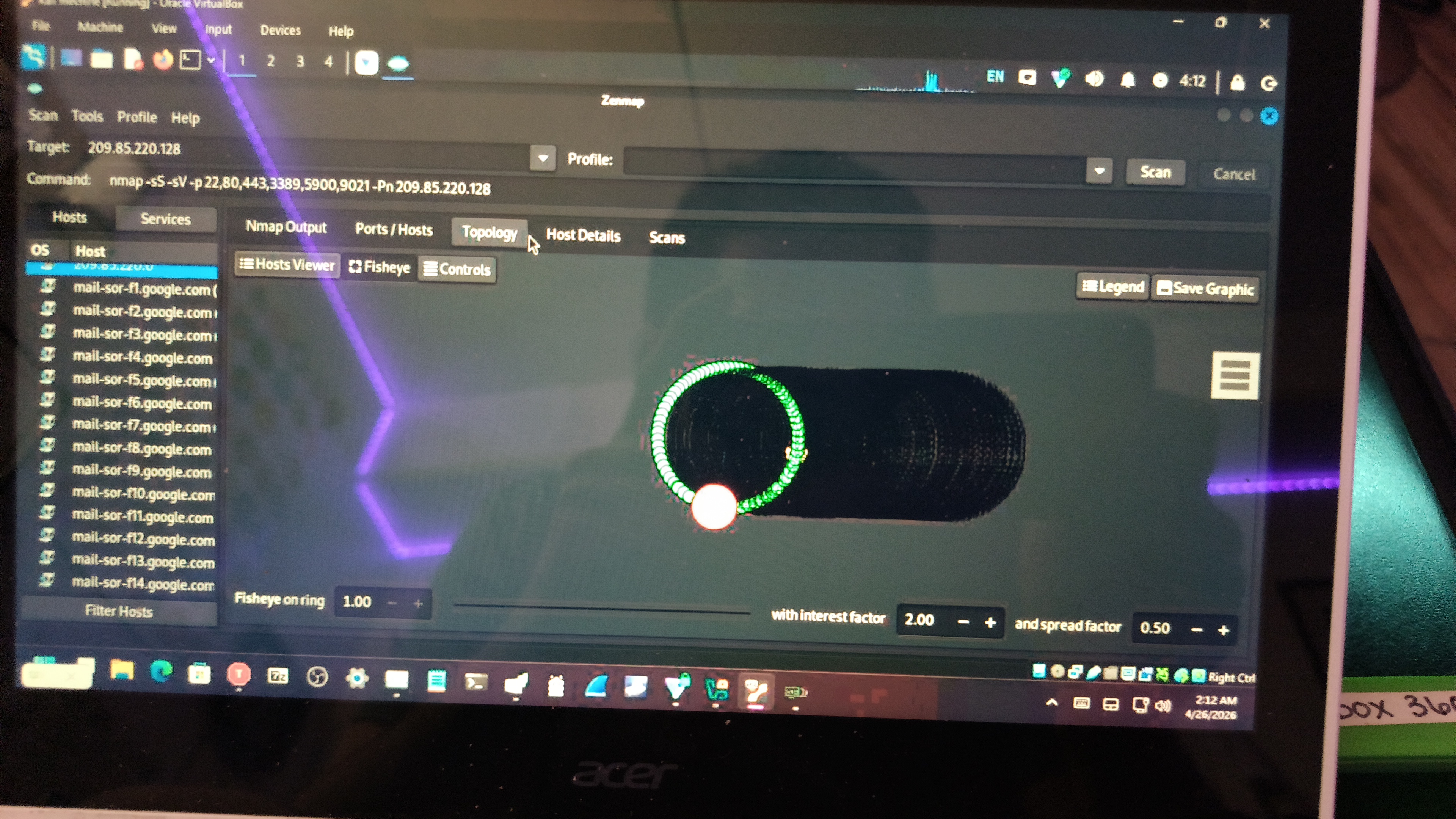
TARGET ASSET: 209.85.220.128
- Status: Active / Human-Operated
- Protocols Detected: RDP (3389), VNC (5900), Remotix (9021)
- Function: Remote Workstation / Victim Interaction Hub
FORENSIC EVIDENCE
Network Topology
Visual mapping of the Google cluster surrounding the target node.
Service Enumeration
Proof of active remote desktop protocols on the "Ghost" host.

CONCLUSION
This investigation proves that scam operations are no longer just using local hardware; they are co-opting high-reputation cloud infrastructure to bypass traditional security filters. Sky Pulse News will continue to monitor this subnet.